A massive, highly
sophisticated piece of malware has been newly found infecting systems in
Iran and elsewhere and is believed to be part of a well-coordinated,
ongoing, state-run cyber-espionage operation.
The Flame computer virus not
only stole large quantities of information from various Iranian
government agencies, but apparently even disrupted its oil exports by
shutting down oil terminals, information security firm Symantec Israel
said yesterday.
The Flame virus recently found
in Iran could be used to infect other countries, according to the
International Telecommunications Union. As the United Nations agency
charged with helping members protect their data networks, the ITU plans
to issue a warning about the danger of Flame.
Iran's National Computer
Emergency Response Team (Maher) said in a statement that the detection
and clean-up tool was finished in early May and is now ready for
distribution to organisations at risk of infection.Flame was discovered
after the UN's International Telecommunications Union asked for help
from security firms to find out what was wiping data from machines
across the Middle East.An investigation uncovered the sophisticated
malicious programme which, until then, had largely evaded detection.
The virus is about 20 times the
size of Stuxnet, malware that targeted the controls of an Iranian
nuclear facility. The largest concentration of infected machines is in
Iran, followed by the Palestinian-controlled West Bank, Sudan, Syria,
Lebanon, Saudi Arabia, and Egypt.
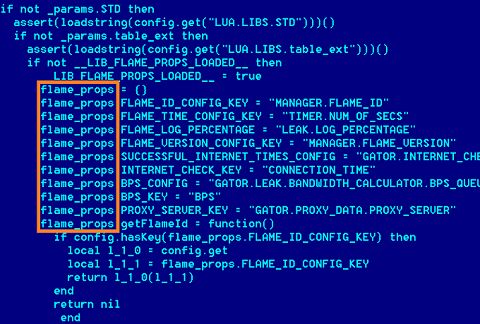
According to the crysys report on sKyWIper (aka Flame):
sKyWIper
has very advanced functionality to steal information and to propagate.
Multiple exploits and propagation methods can be freely configured by
the attackers. Information gathering from a large network of infected
computers was never crafted as carefully as in sKyWIper. The malware is
most likely capable to use all of the computers’ functionalities for its
goals. It covers all major possibilities to gather intelligence,
including keyboard, screen, microphone, storage devices, network, wifi,
Bluetooth, USB and system processes.
Flame is a Swiss Army Knife of
malware in the sense that it can intercept everything imaginable, but it
is not a pile of existing malware code thrown together. It is very
cleverly crafted. Like Stuxnet, it has multiple propagation vectors –
USB keys, printer sharing, and domain controller rights to name a few.
No security vendor has pointed
out a single country or group as being responsible for Flame's
creation.The central matter of contention at the moment is whether the
malware was made by a private group or a nation state.
No comments:
Post a Comment